In its latest release as part of the Vault 7 series, WikiLeaks has apparently leaked a document which consists information regarding a new malware dubbed Pandemic, which is another CIA-built hacking tool.
According to the document:
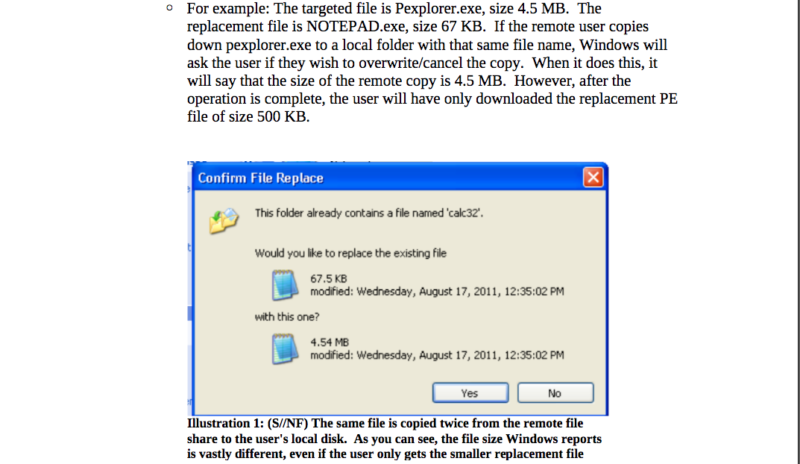
Today, June 1st, 2017, WikiLeaks publishes documents from the “Pandemic” project of the CIA, a persistent implant for Microsoft Windows machines that share files (programs) with remote users on a local network. “Pandemic” targets remote users by replacing application code on-the-fly with a Trojaned version if the program is retrieved from the infected machine. To obfuscate its activity, the original file on the file server remains unchanged; it is only modified/replaced while in transit from the pandemic file server before being executed on the computer of the remote user. The implant allows the replacement of up to 20 programs with a maximum size of 800 MB for a selected list of remote users (targets).
As the name suggests, a single computer on a local network with shared drives that is infected with the “Pandemic” implant will act like a “Patient Zero” in the spread of a disease. It will infect remote computers if the user executes programs stored on the pandemic file server. Although not explicitly stated in the documents, it seems technically feasible that remote computers that provide file shares themselves become new pandemic file servers on the local network to reach new targets.
RELEASE: CIA 'Pandemic' #Vault7 https://t.co/YfxAKT1pog pic.twitter.com/jK8rdFWpCQ
— WikiLeaks (@wikileaks) June 2, 2017
Pandemic and Patient Zero
According to experts, Pandemic is yet another malware that uses the SMB vulnerability found in Windows software to infect computers that share the same local network. As such, the malware can infect an entire network by replacing certain files with the ones that contain Trojans.
The malware has the capability of turning computers into “Patient Zero” machines through the Windows file server. That is, a single computer can be used as a means to infect other computers within the network if the targeted computer downloads the infected file.
How does Pandemic work?
Essentially, the virus does not do anything when it enters a targeted computer. However, when one tries to access a file from the server which has been infected, the file will be automatically replaced with the one that contains the malware.
As such, the malware can infect more than one computer as users download the file from the server or access the file through the network sharing system.
Furthermore, experts say that it is likely that remote computers which share files, can themselves become the pandemic servers and hence hunt down more targets to infect.
The spread can, therefore, be exponential without any stoppage.
Also, it has been stated that Pandemic only takes 15 seconds to get installed in the system as a file system filter driver and that it has the potential to replace 20 files with a total of size of 800 MB at any one time. Also, it is effective against both 34-bit and 64-bit systems.
Nevertheless, the documents do not reveal as to how Pandemic can be installed in the first place.
The leak has been described as the largest ever publication on CIA documents and the documents have their source in CIA’s Center for Cyber Intelligence in Langley, Virginia.
Source: WikiLeaks | Image Credit: Shutterstock/By Bakhtiar Zein
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.